Credential harvesting from browsers and apps — extract saved logins, cookies, autofill data (Chrome, Edge, Firefox, Opera). Modern stealers commonly target browser profiles.
Cookie and session/token theft — steal session cookies and application tokens (Discord, Telegram, Steam) enabling account hijack.
Crypto wallet & seed extraction — search for local wallet files, seed phrases, private keys (browser wallet extensions, desktop wallets).
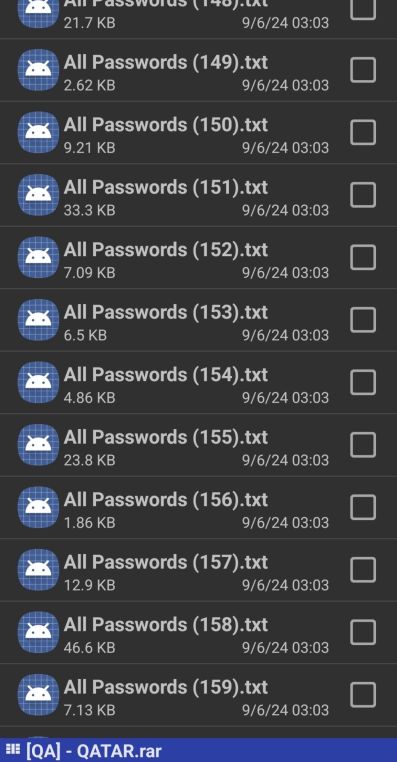
Credential/secret exfiltration — collect credentials, 2FA cookies, and send them back to C2 as “log” files for resale.
File theft or targeted file collection — scan user folders (Desktop, Documents) for file types of interest and exfiltrate.
Keylogging / screenshots — capture keystrokes or periodic screenshots to steal MFA codes or other live data. (Common but not universal.)
Persistence & obfuscation — install as a service/registry autorun, pack/obfuscate the binary, use VM/analysis checks and string encryption to evade detection.
Modular downloader/backdoor capability — some stealers include loaders to fetch additional modules (ransomware, loaders, C2 tools).







You must be logged in to post a comment.