An Irregular Warfare Analysis of the Handala Threat Network
| Primary judgment | Handala is best understood as a public-facing Iranian proxy persona linked to the MOIS-affiliated Void Manticore cluster rather than as an independent hacktivist collective. |
| Confidence | High on state linkage and destructive capability. Moderate on the exact internal chain of command and the full scope of wartime coalition coordination. |
| Main evidence | Greatest weight falls on Check Point, Unit 42, Push Security, the March 2026 DOJ seizure notice, and Stryker’s own public disclosures. |
| Main uncertainty | Public claims released through Handala channels and sympathetic media often outpace what open reporting confirms. Public scale estimates for the Stryker incident also vary. |
Executive Summary
Open reporting supports a high-confidence judgment that Handala functions as a state-directed proxy brand, not as a spontaneous online collective. Check Point ties the persona to Void Manticore, a cluster linked to Iran’s Ministry of Intelligence and Security, and the Justice Department said in March 2026 that MOIS used Handala-linked domains to claim hacks, publish stolen material, and support psychological operations and transnational repression.1,3
Open-source reporting on Handala is uneven. Vendor research gives the clearest picture of tradecraft. Victim disclosures provide the cleanest evidence of business impact. Persona statements and secondary amplification are noisier and sometimes inflated. Judgments in the sections that follow therefore weigh government reporting, victim disclosures, and technical vendor research more heavily than Telegram boasts or wartime rumor.1,3,4,5,6,7,8
Handala and the Void Manticore Cluster
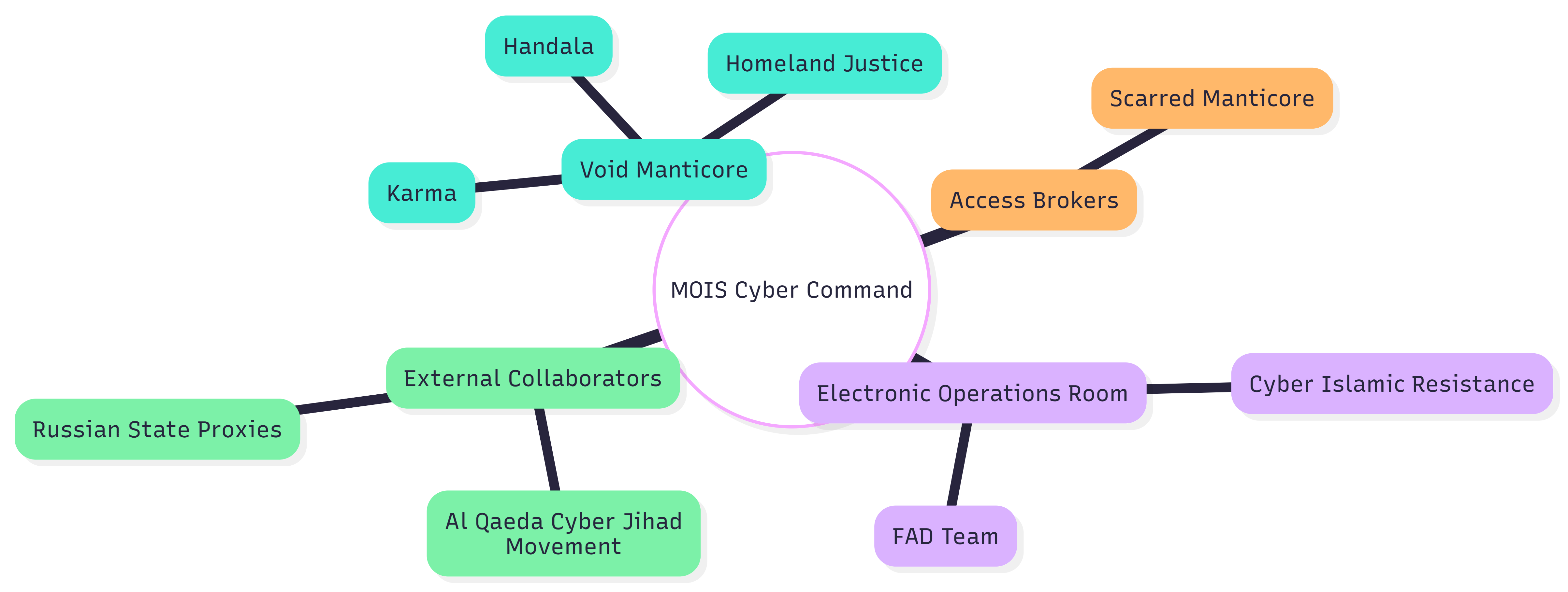
Available reporting points to continuity across Handala, Karma, and Homeland Justice. Check Point traces all three personas to Void Manticore, also tracked as Red Sandstorm, Banished Kitten, and Storm-0842. That continuity matters because it places Handala inside an established state-linked campaign lineage with prior activity in Israel and Albania rather than inside a one-off wartime brand.1,2
The internal command picture is less tidy than the broad attribution. Check Point cites public reporting that links Void Manticore to the MOIS Internal Security Deputy and its Counter-Terrorism Division. DOJ did not publish the same internal naming detail, but its March 2026 seizure notice independently described MOIS use of Handala-linked domains for psychological operations, data publication, and threats of violence. Taken together, the evidence supports high confidence on MOIS linkage and only moderate confidence on the exact supervisory chain.1,3
How the Network Operates
Check Point’s 2024 work described a recurring handoff model between Scarred Manticore and Void Manticore. Scarred Manticore appears to do the patient access work – long dwell time, exfiltration, and quiet positioning – while Void Manticore moves in for the destructive phase. Check Point later found similar patterns in Handala activity, which helps explain how a loud public persona can still reach well-defended targets.1,2
Coalition activity around Handala widened during the March 2026 crisis. Unit 42 reported roughly 60 active hacktivist groups and identified an ‘Electronic Operations Room’ formed on 28 February as a coordination point for multiple Iranian state-aligned personas. GNET, looking at al-Qaeda’s Cyber Jihad Movement, described the same ecosystem as a place where scripts, tooling, and operational cover circulate across ideological lines. Breadth of wartime coordination remains harder to verify than Handala’s core attribution, yet the broader mobilization is well supported.4,12
Figure 1. Reported relationships among MOIS-linked personas, access brokers, and wartime collaborators. The diagram reproduces the structure used in the source draft but is retained here as an analytic aid rather than as independent evidence.
Figure 1. Reported relationships among MOIS-linked personas, access brokers, and wartime collaborators. The diagram reproduces the structure used in the source draft but is retained here as an analytic aid rather than as independent evidence.
Propaganda, Intimidation, and Inflated Claims
Technical intrusion is only one part of the Handala model. DOJ described Handala-linked domains as tools for psychological operations and transnational repression. Public reporting on the March 2026 breach of FBI Director Kash Patel’s personal email account fits that pattern: the incident generated value partly through access and partly through the public theater built around that access.3,10,11
CBS reported that the Patel account held historical personal material and no government information. That distinction matters. Intelligence value, coercive value, and propaganda value are not the same thing. A sound analytic posture separates confirmed access, reported access, and adversary self-description because Handala has strong incentives to compress modest intrusions into a story of omnipresence.10,11
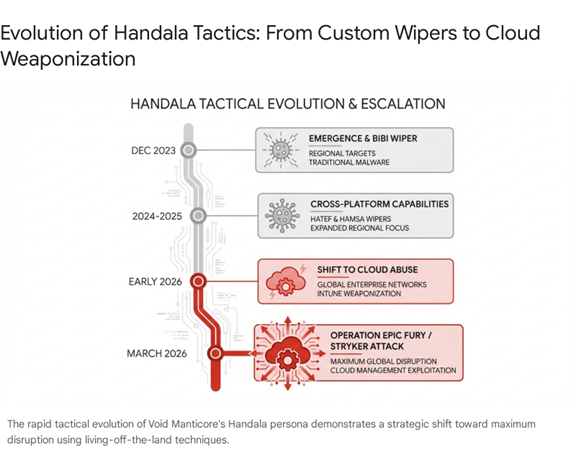
From Wipers to Management-Plane Abuse
Older Handala activity already showed a practical destructive toolkit: hands-on intrusion, lateral movement by Remote Desktop Protocol, Group Policy distribution, and multiple wiping methods running in parallel. Splunk and Cisco Talos assessed with moderate confidence that at least one operator is fluent in Hebrew, which helps explain the quality of some lures. Check Point’s 2026 reporting still found manual movement, NetBird tunneling, credential extraction, and Group Policy abuse in the destructive phase.1,13
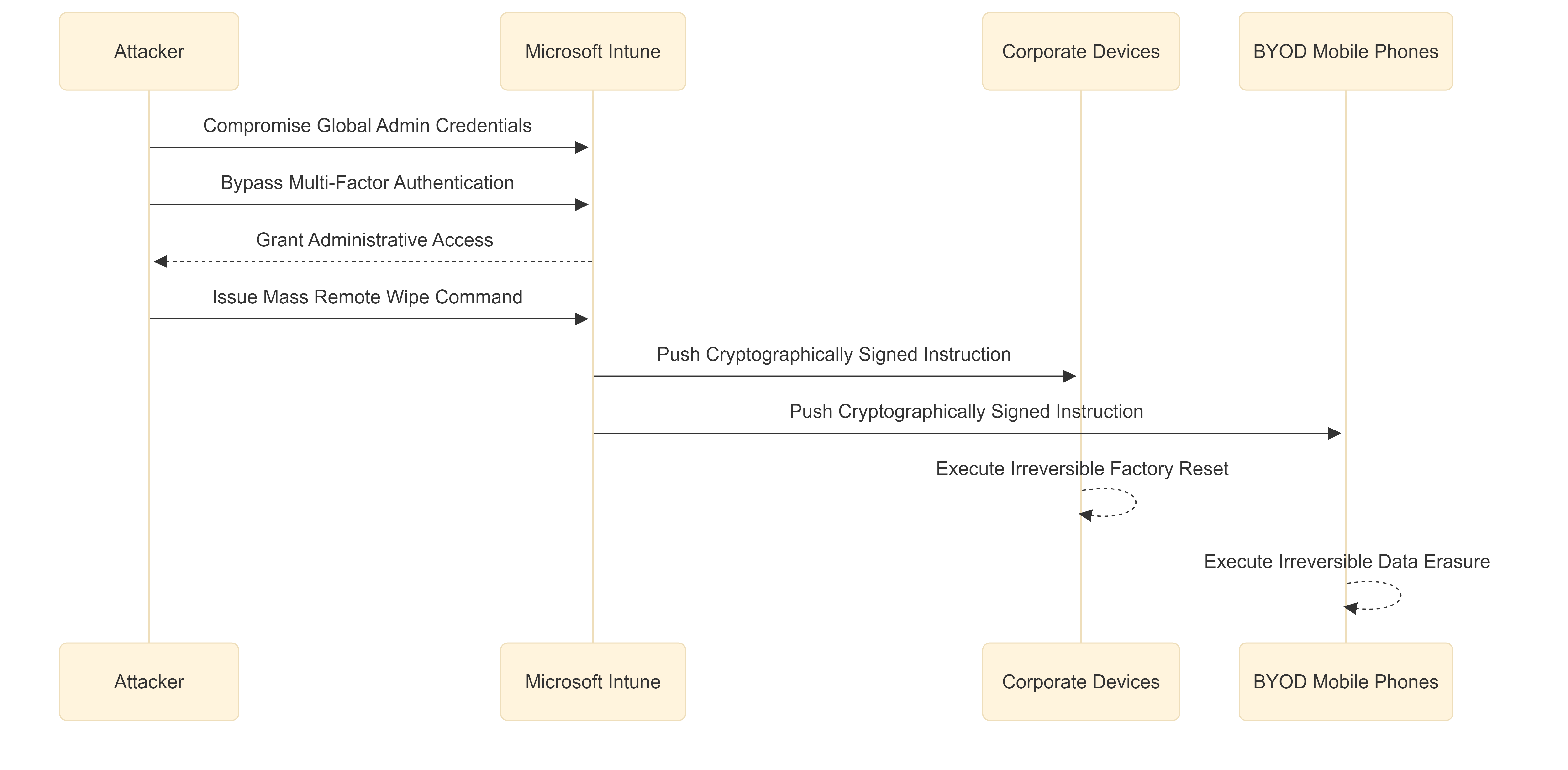
Recent reporting shows a sharper change in where destruction happens. Unit 42 and Push Security each argue that Iranian operators increasingly favor control-plane abuse over custom binaries. Instead of dropping novel malware, the attacker steals privileged identities, logs into trusted management systems, and uses signed remote commands to erase devices at scale. That shift removes one of the old warning signs for defenders: malware on disk.5,6
Figure 2. Simplified sequence of an Intune-enabled remote wipe. The diagram from the source draft illustrates how a privileged identity compromise turns a trusted management service into a delivery path for destructive commands.
The technical point is easy to miss because the mechanism looks ordinary. A remote wipe issued through a legitimate tenant is still a destructive act even when every command is signed and vendor-delivered. Unit 42 described recent Handala-linked incidents as the compromise of highly privileged identities followed by remote-wipe commands pushed to more than 200,000 devices globally. Push Security framed the same pattern as a warning against over-relying on an actor’s historical malware catalog when the management plane itself has become the weapon.5,6
Figure 3. Timeline of Handala’s reported shift from traditional wipers to cloud management abuse. The source figure is retained because it captures the change in emphasis more clearly than the narrative alone.
Figure 3. Timeline of Handala’s reported shift from traditional wipers to cloud management abuse. The source figure is retained because it captures the change in emphasis more clearly than the narrative alone.
Why Stryker Matters
Stryker matters because public evidence exists from the victim, not only from the adversary. The company’s 11 March 2026 Form 8-K said a cybersecurity incident caused a global disruption to Stryker’s Microsoft environment. Stryker’s customer updates later added two points that sharply narrow the analytic lane: the company had no indication of ransomware or malware, and the disruption affected ordering, manufacturing, and shipping while connected medical products remained safe to use.7,8
Third-party estimates of scale vary. Push Security reported abuse of Global Administrator access to Microsoft Intune and described wiped laptops, phones, and servers across 79 countries. Unit 42 wrote that recent Handala-linked incidents involved legitimate remote-wipe commands pushed to more than 200,000 devices globally. Stryker itself has not publicly validated the larger figures, so the safest judgment is narrower: a trusted enterprise management plane was turned into a destructive weapon, and the result was a documented global business disruption without conventional malware.5,6,7,8
Commentary after the incident placed Stryker inside a broader concern set – supply-chain fragility, healthcare disruption, and the chance that the event was an early signal rather than an isolated case. That wider warning is plausible, though still predictive rather than proven. More confidence belongs on the method than on long-range forecasting about what Iran-linked proxies will strike next.9,15
Tradecraft and the Criminal Ecosystem
Handala does not rely only on custom capability. Check Point’s March 2026 reporting placed the persona inside a broader MOIS trend of borrowing from the criminal ecosystem. One example stands out: use of the Rhadamanthys infostealer in phishing lures that impersonated trusted Israeli institutions. Combined with Check Point’s earlier findings on manual operations and Splunk’s reporting on tailored Hebrew lures, the picture is less ‘elite zero-day actor’ than disciplined operator willing to mix state direction with commercial tooling.2,13,14
That mix has analytic consequences. Commodity tools and common access methods do not argue against state direction in this case. On the contrary, cheap tools, deniable personas, and outside access support appear to be part of the operating model. Iran-linked actors gain cover, scale, and speed while preserving enough ambiguity to muddy public attribution.1,14
Observed destructive methods in recent Handala reporting
| Method | Where observed | Delivery path | Likely effect |
| Manual intrusion plus RDP movement | Check Point 2024-2026 | Hands-on access, local tools, direct operator control | Long dwell time, selective targeting, faster destructive follow-on |
| Group Policy and scheduled tasks | Check Point 2026 | Domain-level distribution of wipe components and scripts | Parallel execution across many hosts and harder recovery |
| NetBird tunneling | Check Point 2026 | Operator-created internal reach to systems not exposed externally | Faster lateral movement and multi-foothold control |
| Intune remote wipe | Push and Unit 42, March 2026 | Compromise of privileged identities in MDM or cloud control plane | Authenticated factory reset at global scale without malware on disk |
Table 1. Methods that recur across recent reporting. The table emphasizes delivery path and effect rather than chasing every reported malware family.
Defensive Implications
The defensive lesson is plain. Control-plane security and identity governance now sit on the same line as endpoint defense. Hardware-backed authentication for high-privilege accounts, conditional access, tighter admin segmentation, and well-tested offline recovery are no longer background hygiene items. They are continuity controls.5,6,8
Recovery planning also needs a narrower operational focus than many organizations give it. Stryker’s public updates show how a corporate Microsoft disruption spills into ordering, manufacturing, and customer communication even when core products stay safe. Backup success alone is not enough. Organizations need to know how they will keep shipping, paying staff, authenticating users, and communicating with customers while the management plane is down.7,8
Conclusion
Handala matters less because of any single wiper family than because it shows how a state proxy can turn routine enterprise administration into a coercive instrument. The network combines state alignment, proxy branding, intimidation, and destructive access in a form well suited to irregular conflict. Older warning models looked first for malware samples and network signatures. Recent reporting suggests the more important indicator now sits one layer higher: who controls the identities, consoles, and trust relationships that run the enterprise.1,3,5,7
Strong open-source work already exists on the network. Better analysis starts by ranking sources correctly, resisting persona hype, and separating confirmed business impact from adversary theater. Once that discipline is in place, Handala reads less like a chaotic hacktivist brand and more like a durable Iranian proxy model built to blend sabotage with psychological pressure.1,3,4
References
- Check Point Research. “Handala Hack” – Unveiling Group’s Modus Operandi. 12 March 2026. https://research.checkpoint.com/2026/handala-hack-unveiling-groups-modus-operandi/
- Check Point Research. “Bad Karma, No Justice: Void Manticore Destructive Activities in Israel.” 20 May 2024. https://research.checkpoint.com/2024/bad-karma-no-justice-void-manticore-destructive-activities-in-israel/
- U.S. Department of Justice. “Justice Department Disrupts Iranian Cyber Enabled Psychological Operations.” 19 March 2026. https://www.justice.gov/opa/pr/justice-department-disrupts-iranian-cyber-enabled-psychological-operations
- Palo Alto Networks Unit 42. “Threat Brief: March 2026 Escalation of Cyber Risk Related to Iran (Updated March 26).” 26 March 2026. https://unit42.paloaltonetworks.com/iranian-cyberattacks-2026/
- Palo Alto Networks Unit 42. “Iranian Cyber Threat Evolution: From MBR Wipers to Identity Weaponization.” 16 March 2026. https://unit42.paloaltonetworks.com/evolution-of-iran-cyber-threats/
- Push Security. “The Stryker breach didn’t match the playbook. That shouldn’t be a surprise.” 19 March 2026. https://pushsecurity.com/blog/stryker-handala-report
- Stryker Corporation. Form 8-K, filed 11 March 2026. https://www.sec.gov/Archives/edgar/data/310764/000119312526102460/d76279d8k.htm
- Stryker. “Customer Updates: Stryker Network Disruption.” March 2026 updates. https://www.stryker.com/us/en/about/news/2026/a-message-to-our-customers-03-2026.html
- Krebs on Security. “Iran-Backed Hackers Claim Wiper Attack on Medtech Firm Stryker.” 11 March 2026. https://krebsonsecurity.com/2026/03/iran-backed-hackers-claim-wiper-attack-on-medtech-firm-stryker/
- PBS NewsHour. “Pro-Iranian group claims credit for hacking into FBI Director Patel’s personal account.” 27 March 2026. https://www.pbs.org/newshour/nation/pro-iranian-group-claims-credit-for-hacking-into-fbi-director-patels-personal-account
- CBS News. “FBI Director Kash Patel’s personal email breached by hackers linked to Iran, sources say.” 27 March 2026. https://www.cbsnews.com/news/fbi-director-kash-patel-email-hackers-lran/
- Global Network on Extremism and Technology. “Al-Qaeda’s Cyber Jihad Movement: Plugging into Iran’s Wartime Hacktivist Ecosystem.” 23 March 2026. https://gnet-research.org/2026/03/23/al-qaedas-cyber-jihad-movement-plugging-into-irans-wartime-hacktivist-ecosystem/
- Splunk Threat Research Team and Cisco Talos. “Handala’s Wiper: Threat Analysis and Detections.” 6 September 2024. https://www.splunk.com/en_us/blog/security/handalas-wiper-threat-analysis-and-detections.html
- Check Point Research. “Iranian MOIS Actors & the Cyber Crime Connection.” 10 March 2026. https://research.checkpoint.com/2026/iranian-mois-actors-the-cyber-crime-connection/
- Nextgov/FCW. “Stryker hack could set stage for more pro-Iran cyber sabotage.” 13 March 2026. https://www.nextgov.com/cybersecurity/2026/03/stryker-hack-could-set-stage-more-pro-iran-cyber-sabotage/412115/