Recent Arrests of Suspected Iranian Spies

Israeli authorities have exposed a series of espionage cases involving local citizens allegedly recruited by Iranian intelligence. In late June 2025, an Israeli couple in their 30s from the city of Ra’anana was arrested on suspicion of spying for Iran. Detectives from the Israel Police Central District, in cooperation with the Shin Bet security agency, conducted a covert investigation and raided the couple’s home. They seized several mobile phones, computers, and other electronic devices, discovering correspondence believed to be between the couple and an Iranian handler. The unnamed husband and wife were brought before a court the next day for a custody hearing on these serious allegations.
The arrest came shortly after another announcement in which three Israelis were detained in two separate espionage cases connected to Iran. The quick succession of arrests within 24 hours underscored an upsurge in Iranian spy activity being detected in Israel. Police and Shin Bet officials indicated these individuals conducted various tasks assigned by Iranian agents, ranging from intelligence gathering to planning violent missions. Israeli security forces are treating these cases as part of a broader Iranian effort to infiltrate and weaken Israel from within amid heightened regional tensions.
Espionage Case 1: Ra’anana Couple and Covert Communications
Investigators have released limited details about the Ra’anana couple’s alleged activities, as much of the case remains under gag order. Evidence gathered in the raid suggests the couple had been in direct communication with Iranian intelligence operatives. The pair reportedly exchanged messages with a clandestine handler, who provided instructions and received updates in return. The content of these communications has not been fully disclosed, but officials say it clearly shows espionage-related coordination with a hostile foreign agent. The presence of multiple phones and encrypted devices in their apartment indicates a strategic attempt to maintain secrecy and avoid detection.
Law enforcement noted that this investigation began only about a week before the arrests, implying that Israeli intelligence had picked up on the suspicious communications relatively quickly. The Shin Bet and police likely monitored the couple’s interactions in real time once alerted. By acting swiftly, authorities were able to catch the suspects by surprise and secure physical evidence of their secret correspondence. This quick operation prevented any further damage that prolonged spying might have caused. The couple’s case highlights how Iranian agents may try to cultivate assets even in well-to-do, quiet communities (Ra’anana is a suburban city) and how rapidly Israeli counterintelligence can mobilize once a lead is identified.
Police displayed items obtained from the Ra’anana couple’s home, including phones, cash, and computers, after the raid. (An image released by Israel Police shows an array of smartphones, stacks of money, and electronic devices laid out on a table — all items investigators confiscated as suspected espionage tools.) These tangible clues bolster the case that the couple knowingly exchanged information with Iranian handlers and perhaps received payment for their services.
Espionage Case 2: Grenade Smuggling and Intelligence Gathering
Authorities reported that a 33-year-old Israeli man from the Jordan Valley was arrested for carrying out dangerous missions for Iran. The suspect, identified in media reports as Mark Morgein (also reported as Mark Morgan in some sources), allegedly accepted assignments from an Iranian intelligence handler throughout June 2025. One of his responsibilities involved a mission to deliver weapons. He was directed to a secret location in the West Bank to retrieve a concealed hand grenade and transport it to another designated drop point. By doing so, he knowingly acted as a courier for an explosive device that Iranian agents intended to use in an attack on Israeli civilians. Security officials emphasize that the suspect understood the grenade he was transporting was meant to cause harm, indicating a willful complicity in a potentially deadly scheme.
Another mission conducted by this operative was surveillance of Israel’s air defenses. He was tasked with filming a video of a missile interception and sending it to his Iranian handler. This incident took place during a recent conflict dubbed “Operation Rising Lion,” a 12-day flare-up that saw Iranian missiles fired toward Israel. The arrested man used his proximity to an interception site to capture footage of Israel’s air defense response. Intelligence experts assess that Iranian planners sought such footage to study the performance of systems like Iron Dome and refine their offensive tactics. A Reuters photograph from that period shows Israeli air defense missiles streaking skyward from the West Bank, intercepting incoming Iranian projectiles – an image that shows the broader context of Iran’s direct hostility during that conflict. The fact that an Israeli citizen was allegedly gathering visual intelligence on missile interceptions for Iran is a striking example of domestic espionage directly supporting enemy military operations.
Following his arrest, a magistrate’s court extended the suspect’s detention, and investigators indicated that formal charges would be forthcoming. The swift apprehension likely prevented the grenade from being handed off to its intended recipient and thwarted any immediate plots to use it. It also sent a strong message that even seemingly low-level tasks—such as couriering a weapon or filming a rocket interception—are being closely monitored and will lead to severe consequences. Israeli authorities treat such acts as aiding the enemy in wartime. A possible attack within Israel was prevented by stopping this operative.
Espionage Case 3: Tiberias Duo and Assassination Plot
The third case unveiled involves two young men from Tiberias, aged 18 and 20, who were arrested on suspicion of collaborating with Iranian intelligence in a bold and disturbing plot. Yoni Segal and Nehorai Omri Mizrahi were allegedly recruited over the past two months and assigned a mission to target an Israeli individual in exchange for a significant amount of money. According to the Shin Bet’s findings, an Iranian agent offered to pay them hundreds of thousands of shekels for the hit. The handler even laid out an elaborate plan: the pair were instructed to travel to an unspecified foreign country, where they would receive weapons training and further instructions, after which they would be provided with the identity of the person they were to kill. The plan was an exceptionally audacious assignment, showing that Iranian operatives were testing whether they could not only gather intelligence but also orchestrate lethal attacks inside Israel using locally recruited agents.
Fortunately, this assassination plot never came to fruition. Israeli security forces moved in and arrested Segal and Mizrahi before they could leave the country for their training abroad. By preempting their departure, the Shin Bet stopped the plot at an early stage. Investigators have not publicly revealed who the intended victim was, but the circumstances suggest it may have been a high-value target (such as a public official or a person in the security establishment), given the promised payment and training involved. The case marks a significant escalation from intelligence gathering to direct terrorist action under Iranian direction.
In addition to the thwarted assassination attempt, the Tiberias pair is also alleged to have carried out extensive surveillance on civilian targets throughout Israel in cooperation with the Iranian agent. For weeks, they allegedly filmed and mapped out several busy public venues: shopping malls and a major hospital. Among the locations they covered were the Grand Canyon Mall in Haifa, the Big Fashion Mall in Tiberias, Tel Aviv’s iconic Dizengoff Center, and areas around Tel Aviv’s Ichilov (Sourasky) Medical Center. They documented details such as each site’s layout, the number of stores, and the security measures or guards present. This information was conveyed to their Iranian contact. At one point, the young operatives even sent their live GPS locations to prove they were at the targets and to request further instructions, demonstrating their eagerness to continue with the assignments.
These activities mirror reconnaissance work typically done in preparation for potential terrorist attacks. Gathering such inside details on public places would be invaluable for planners seeking to maximize casualties or choose vulnerable targets. For instance, understanding security guard routines and structural layouts could help attackers evade detection or decide where to place explosives for maximum impact. The inclusion of a hospital in their assignment is particularly chilling, as it suggests no location was off-limits. The Shin Bet considers these surveillance missions compelling evidence of hostile intent – the Iranian agent was systematically collecting intelligence on Israeli civilian infrastructure through these recruits.
Upon their arrest, Yoni Segal and Nehorai Mizrahi were brought before a court, where a judge extended their detention by at least four days while the investigation continues. The suspects will soon face serious charges. Their case highlights how Iranian intelligence is willing to exploit even teenagers or very young adults, grooming them with promises of adventure and financial reward to conduct dangerous spying missions. It also demonstrates the growing boldness of Iran’s plans, moving beyond surveillance to attempting to instigate violent attacks inside Israel.
Iranian Recruitment Methods and Espionage Patterns
Israeli intelligence officials stress that these incidents are not isolated, but rather part of a pattern of Iranian espionage efforts that has intensified in recent years. Tehran’s security agencies – including the IRGC (Islamic Revolutionary Guard Corps) and MOIS (Ministry of Intelligence) have developed aggressive tactics to recruit Israeli citizens as assets. Often, initial contact with a potential recruit occurs online. A Shin Bet report from late 2023 revealed that Iranian operatives have been reaching out to Israelis on social media platforms (such as Telegram, WhatsApp, Facebook, Instagram, and X/Twitter) under false identities. They typically masquerade as ordinary people or business contacts – for example, posing as real estate agents, import-export dealers, prospective employers, or even as suitors on dating apps. The goal is to build trust through casual conversation before broaching the idea of clandestine “missions.”
Once an operative has engaged an Israeli in dialogue, the offer of money in exchange for small favors soon follows. The Shin Bet reports that Iranian handlers often offer small tasks, such as taking photos, verifying addresses, or gathering public information, for modest payments. At first glance, these requests might appear harmless and unrelated to security, so the target person might rationalize that there is no real harm in earning easy money. Each task aims to meet Iranian intelligence needs and enhance their existing information, according to Shin Bet. For example, asking for photos of a public building or mall might be a test of the recruit’s willingness and also yield fresh images and details for Iran’s operational planning. As seen in the current cases, what began as taking videos or moving objects on command can escalate to far more dangerous assignments over time (like transferring weapons or targeting individuals).
Israeli counterintelligence officials have seen that Iran’s recruitment efforts surged during periods of conflict, exploiting the chaos and distractions of war. In the wake of the October 2023 war in Gaza and subsequent regional clashes, Iran significantly stepped up attempts to enlist Israelis to spy or even commit violence. The Shin Bet noted a marked rise in online approaches to Israeli citizens after that war began. Tehran likely calculates that wartime conditions might make some Israelis more susceptible, either due to financial stress, ideological radicalization, or simply the difficulty of monitoring every communication during a national emergency. The arrests in 2025 underscore that Iran has continued to pursue “spy recruitment at scale” well into the prolonged security crisis, trying to capitalize on any opportunity to sow instability within Israel.
Notably, the methods used in these recent cases closely resemble prior Iranian spy rings that Israel has busted. A notable case occurred in January 2022, where four Israeli women, along with one of their husbands, faced charges of espionage for Iran. In that affair, an Iranian operative using the alias “Rambod Namdar” spent years grooming Israeli Jewish women on Facebook by pretending to be a Jewish man in Iran who was friendly and in need of help. After establishing an online friendship, he persuaded them to perform tasks for money. The assignments echo what is seen in 2025: one woman was paid to photograph the U.S. Embassy in Tel Aviv and a shopping center, while noting the site’s security arrangements. Another was asked to encourage her son to join Israeli military intelligence and even sent the handler photos of his ID badges. Some were told to contact Israeli public figures or share personal details about officials. Although the spy network was eventually identified and dismantled by the Shin Bet, it acted as a significant alert. Iranian intelligence demonstrated a willingness to invest time and resources into cultivating sources inside Israel, even among citizens with no obvious access to state secrets. The 2022 case also proved that financial incentives and skillful deception could lure Israelis into betraying their country’s trust.
The consistent thread through these cases is Iran’s strategic objective: to gather tactical intelligence and foment terrorism within Israel using local agents. Every piece of information gleaned, whether photos of a mall’s layout, video of a missile defense launch, or knowledge of where a grenade might be stored, can feed into larger plans to harm Israeli civilians or military targets. By recruiting Israelis, Iran gains eyes and ears on the ground in a way that remote operatives or satellites cannot easily match. Local recruits can move around freely in Israeli society without arousing suspicion, which is invaluable for reconnaissance or positioning weapons. Additionally, if an Israeli citizen conducts an attack or facilitates one, it might evade initial suspicion or sow internal confusion and mistrust. This modus operandi is part of Iran’s asymmetrical warfare approach, seeking to hit Israel indirectly and deniably.
Implications and Israel’s Response
The uncovering of these espionage plots carries several urgent implications for Israeli security and society. First, the fact that Iranian intelligence was able to find willing collaborators inside Israel, including a married couple in a quiet town and impressionable youths, is a sobering development, showing the need for continued vigilance among the public. Security officials have reiterated their calls for Israelis to be cautious about unsolicited online communications. An innocuous Facebook message or WhatsApp chat from a stranger might be the first step in an Iranian recruitment operation. In the 2022 spy case, then-Prime Minister Naftali Bennett warned citizens to be cautious of suspicious approaches on social media, noting that Tehran often lurks behind content that people casually encounter or share online. That advice remains highly relevant today. Awareness campaigns and public reporting of unusual contact can help nip espionage attempts in the bud – indeed, the Shin Bet has credited some alert Israelis with coming forward when a situation felt off, enabling security services to intervene.
Secondly, these cases suggest that Iran is undeterred and even escalating its espionage ambitions against Israel. The inclusion of a proposed assassination and the handling of actual weaponry (the grenade) represent a more aggressive push than previously seen in many foiled plots. Iranian agents appear emboldened to orchestrate direct attacks inside Israel, not just gather information, fitting with Iran’s broader campaign of proxy terror and covert action aimed at destabilizing Israel amid ongoing conflicts. Israeli defense analysts interpret the 2025 plots as an extension of Iran’s multi-front pressure strategy: while Iranian-supported forces like Hezbollah and Islamic Jihad confront Israel externally, Iranian intelligence tries to open an internal front by subverting Israeli citizens. It poses a complex challenge, as the threat may come from ordinary Israelis who have been co-opted rather than identifiable enemy operatives.
In response, Israeli authorities are likely to intensify counter-espionage measures. The Shin Bet will continue investing in cyber monitoring to track attempts by foreign agents to contact Israelis. Borders might increase screening, especially for young individuals taking unusual last-minute trips that could be related to hostile training. Law enforcement is expected to press charges that carry heavy penalties to deter would-be spies. Charges such as contact with a foreign agent, espionage, conspiracy, and aiding the enemy during wartime could be filed in these 2025 cases, each carrying severe penalties. Publicizing the arrests and the details serves another purpose: it sends a message to Iran that their activities are exposed, and to Israeli citizens that anyone considering such collaboration will be caught and punished.
Ultimately, these revelations may prompt the Israeli security services to enhance their education and resilience programs. Communities must be vigilant for neighbors engaging in suspicious or unusual activities. Families and educators could play a role in warning young people, in particular, about the dangers of online entrapment by hostile actors. An 18-year-old was almost drawn into an assassination plot. Strengthening the societal fabric against such manipulation is now a priority.
Israeli officials emphasize that while the recent spy suspects have been apprehended, the threat from Iran’s espionage network remains ongoing. The pattern of incidents suggests that there are likely other individuals under surveillance or investigation for similar contacts with Iranian handlers. As Iran continues its regional confrontation with Israel, it will persist in seeking covert assets within the country. The Israeli security establishment is on high alert to this risk. Every successful interdiction, such as the Ra’anana couple and the other three suspects, not only prevents an immediate threat but also yields valuable intelligence about Iran’s methods, helping to thwart future plots.
The discovery of these espionage cases is a stark reminder of the shadow war being waged beyond the battlefield. Iranian intelligence operatives are actively targeting Israelis from all walks of life, attempting to turn them into instruments against their nation. Counterintelligence efforts have prevented several potentially harmful plans from being carried out. However, the persistence of such cases means Israel must remain ever watchful. By combining rapid operational response (raids and arrests), public awareness, and international intelligence-sharing, Israeli authorities aim to stay one step ahead of Iran’s espionage apparatus.
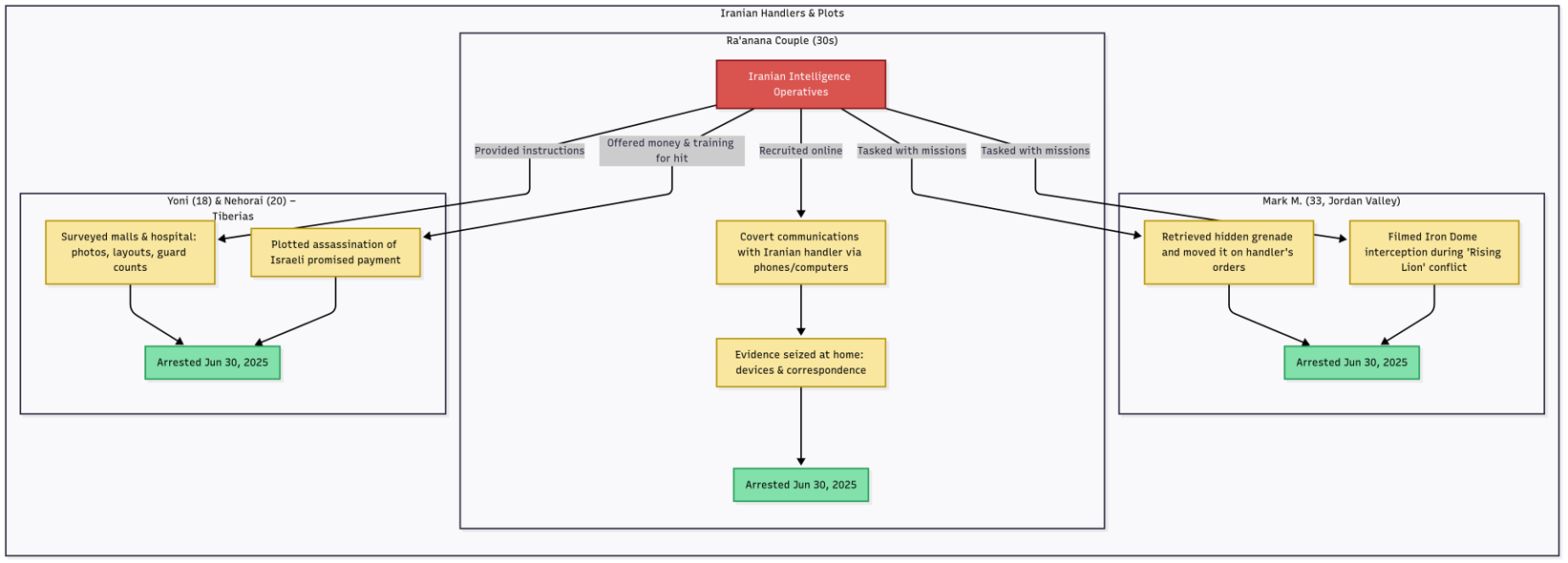
Figure: A diagram of the Iranian espionage network exposed in mid-2025. Iranian handlers (top) recruited multiple Israeli citizens in separate cells (each box). The Ra’anana couple communicated with handlers and were caught with devices containing clandestine correspondence. Mark M. conducted missions, such as moving a hidden grenade and filming a missile interception, before his arrest. The Tiberias duo gathered surveillance on public venues and even prepared for an assassination plot at their handler’s behest. All suspects were arrested in late June 2025, thwarting the potential attacks and intelligence breaches. The diagram highlights how a single foreign adversary (Iran) can manage several local agents in parallel, assigning each different tasks toward the same goal of undermining Israel’s security.



You must be logged in to post a comment.