Cyber Av3ngers released a propaganda-intimidation hybrid targeting Iranian opposition-linked individuals using a blend of personalized threat messaging and psychological pressure. The group aims to silence dissent, project cyber capacity, and frame their narrative within anti-Zionist, anti-Western ideological warfare. The messaging aligns with IRGC-QF front behavior, reinforcing Tehran’s asymmetric retaliation doctrine via cyber and influence vectors.
The poster identifies six individuals by name and face, including Mehdi Ledsghiyan, Mohammad Reza Lotfi Kiani, Meysam Hashemi, Bugher Shirakar, and Amir Salehian. Their identities have been “profiled,” suggesting they are under digital and potentially physical surveillance. The image implies an intelligence dossier has been assembled against them. The message references Nariman Gharib, a known Iranian dissident and digital activist, as the recipient of the threat email.
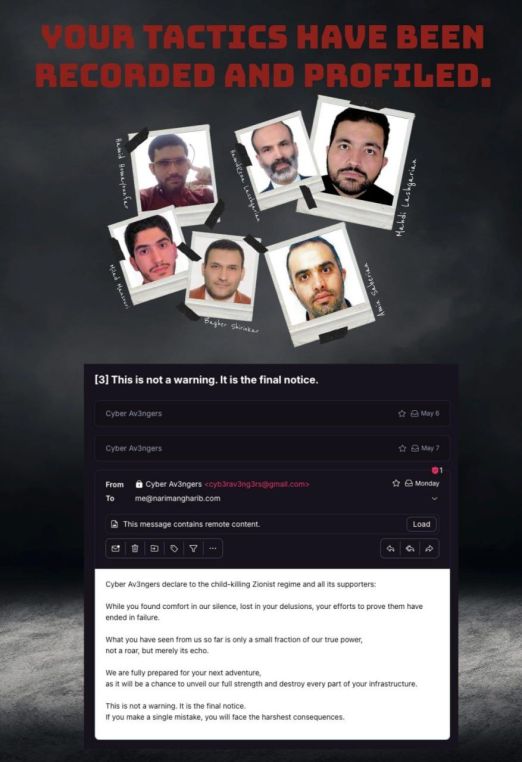
This is a hostile cyber-influence operation integrating a direct threat with active psychological targeting. The email excerpt, stylized for theatrical intimidation, declares the end of passive observation and the transition to punitive action should “a single mistake” occur. The campaign draws on IRGC disinformation tropes such as “Zionist regime” and the child-killer framing to justify potential escalation.
The operation shows signs of advanced profiling, information operations coordination, and psychological targeting aimed at exiled Iranian actors or regime opposition. It functions on two layers: internal deterrence against defection and external messaging to cyber adversaries. This shows state-sanctioned hybrid operators moving from denial-plausible hacks to explicit digital intimidation.
Timing suggests a counter-narrative to increasing Iranian dissident activities online and intensified exposure of IRGC-QF overseas operations. As exiled journalists and cyber activists raise visibility on Iranian proxy networks and cyber campaigns, Tehran’s assets respond with retaliatory targeting via influence operations. The Cyber Av3ngers group likely reflects a rebrand of past Iranian APT psyops teams like Charming Kitten (APT35) with a public-facing agitprop identity.
Such messaging seeks to generate fear, stall opposition reporting, and test psychological thresholds before kinetic or cyber sabotage actions. The integration of personalized emails, names, and public doxing makes this a psychological destabilization attempt—a hallmark of Iranian cyber-pressure campaigns.
Expect more cross-channel hybrid threat dissemination from Iranian-linked cyber units, especially targeting dissidents in Europe and the U.S. Tehran will escalate non-kinetic operations when diplomatic pressure intensifies, framing its asymmetric response as legitimate resistance. This threat vector blends cognitive warfare, offensive counterintelligence, and psychological disruption. The trend line shows increased confidence in psychological warfare tactics tied to cyber operations.
The email and threat do not reflect autonomous hacktivist sentiment but instead demonstrate coordinated state-level narrative warfare. The syntax and ideological framing point to script-heavy information operations standard in Iranian cyber doctrine. The threat uses ambiguity in action (a “mistake” undefined) to maximize paranoia and emotional disruption. The use of English with polished structure, combined with stylized graphics and direct targeting, also seeks Western press coverage and intimidation within diaspora circles. Strategic ambiguity in capacity claims masks the real intent—digital coercion through narrative dominance.






You must be logged in to post a comment.